[ Selected Works ]
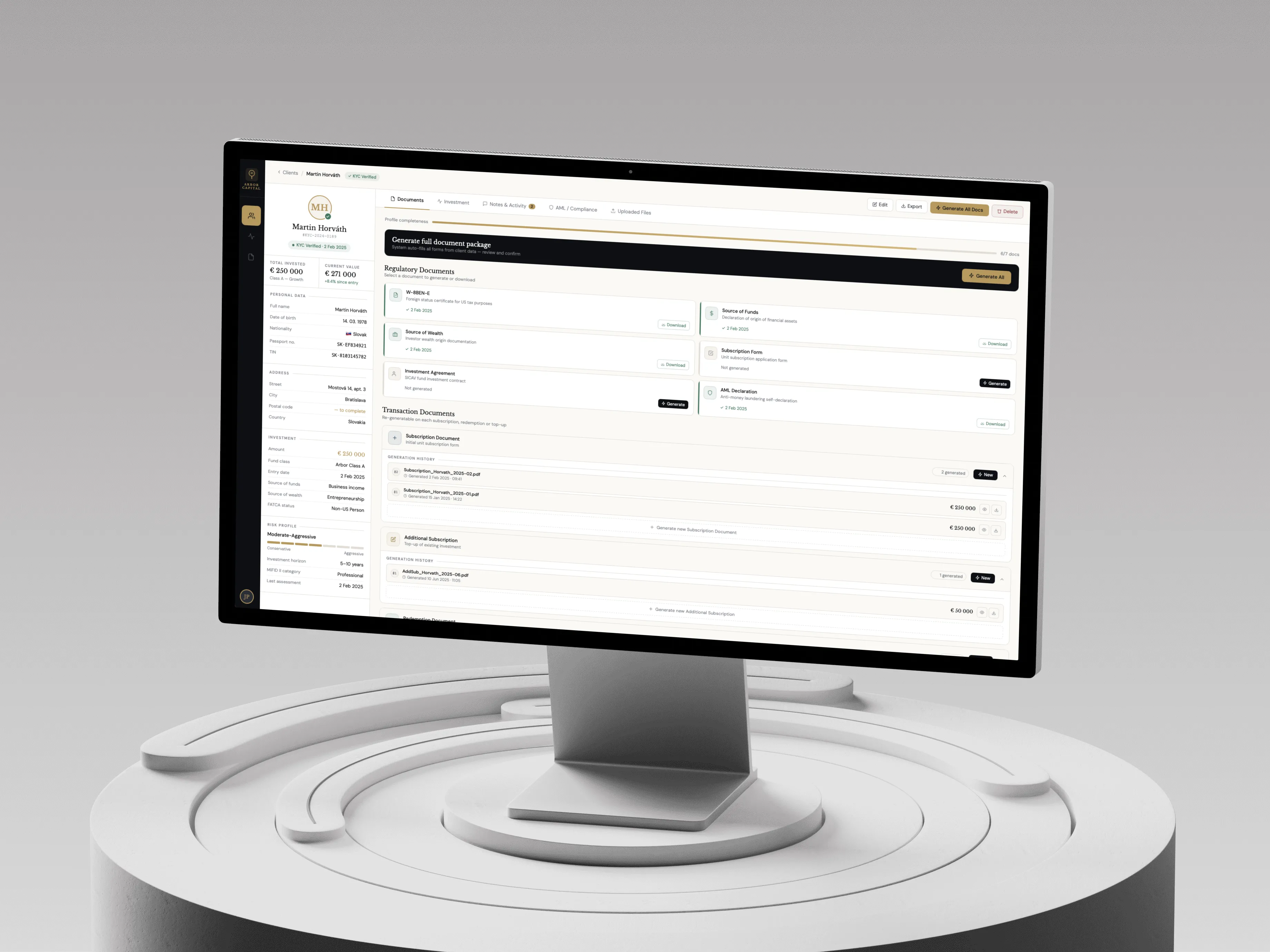
"We didn't start as developers who learned finance. We started as financiers who learned to build."
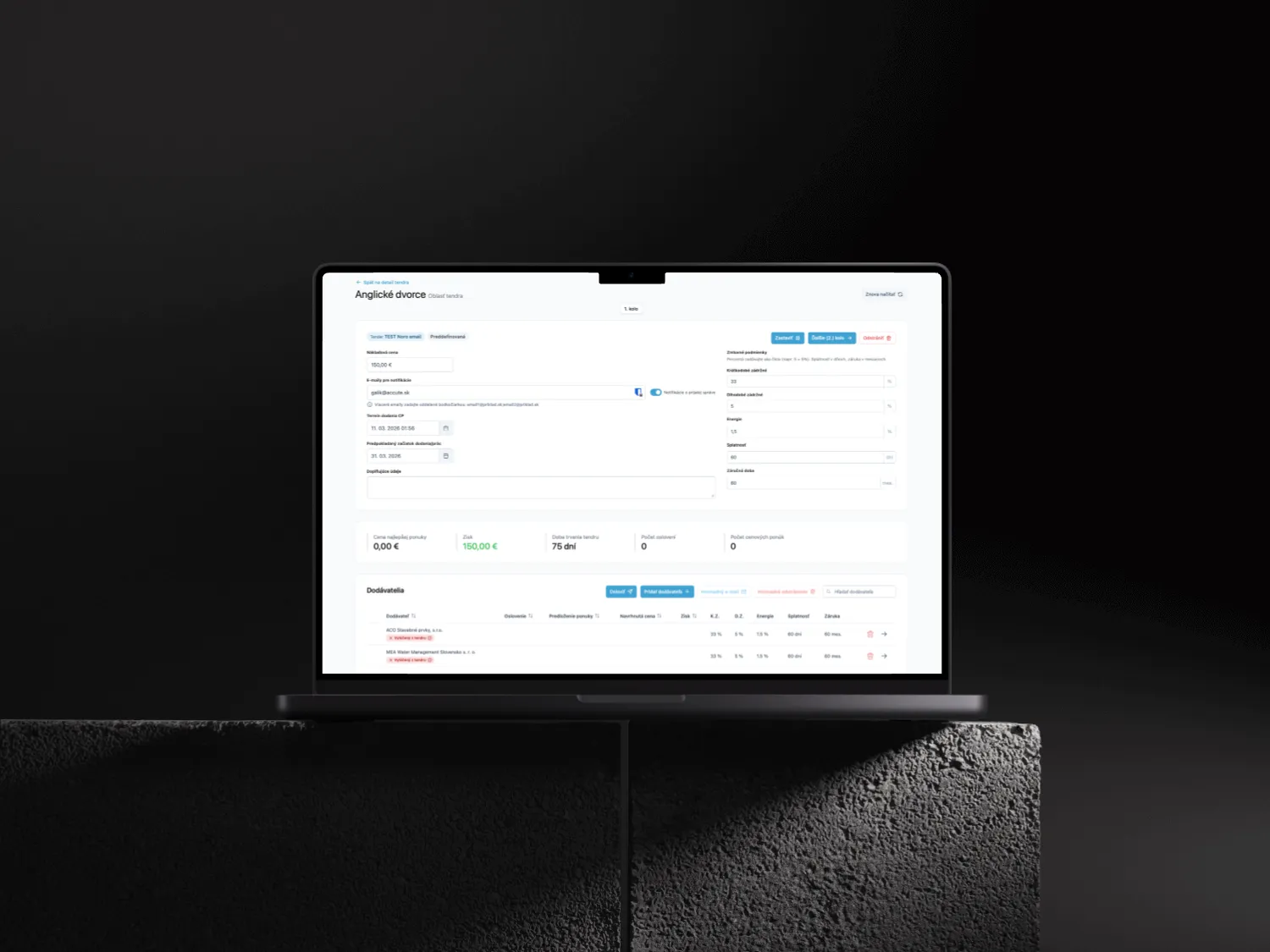
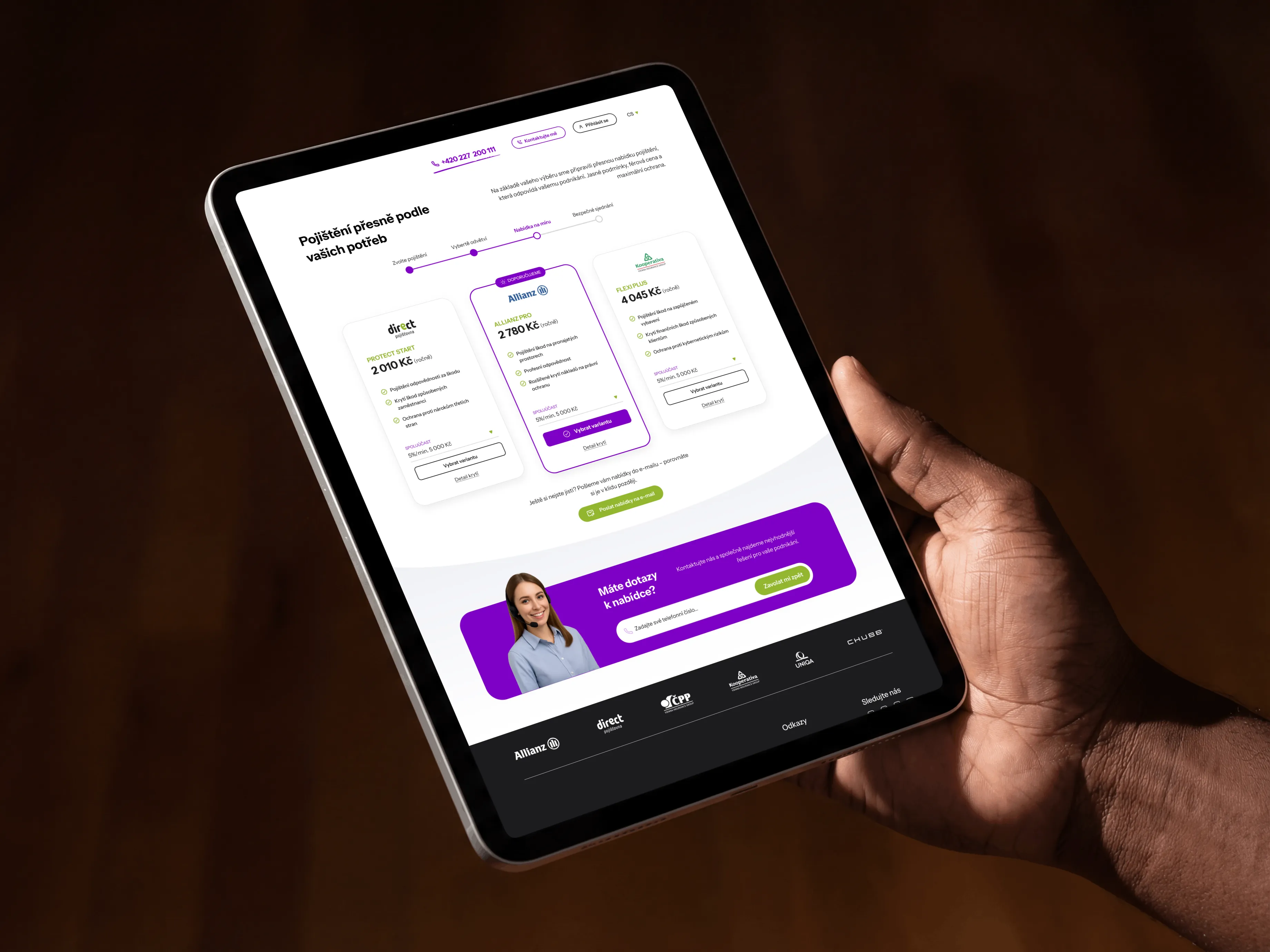
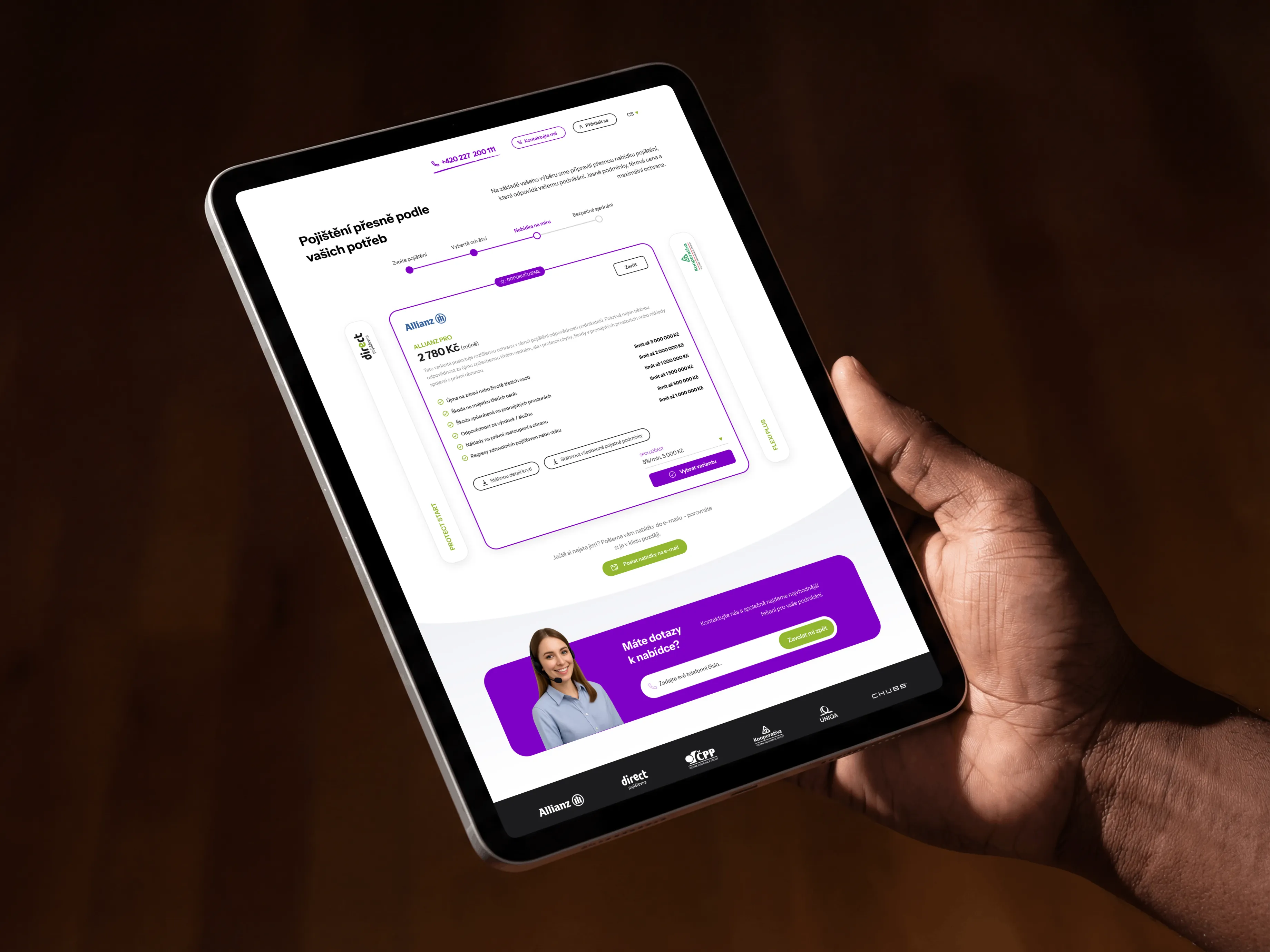
Every system on this page is in production. Infrastructure that runs daily operations for regulated institutions, processes real transactions and has never had a security incident.
From fintech infrastructure to enterprise platforms - every engagement starts with understanding the business, not the brief.
[ BUILT FROM THE INSIDE ]